Operations
Be careful about “fixing” problems in your logs
by Andrew Macpherson on Jan.02, 2014, under Operations
One of the things that happens every night on a Linux server is the administrator gets an emailed log file summary from a process known as “Logwatch” with lots of useful information such as a list of sites that have tried to guess passwords, hack your web server and so on. It also tells the current disk usage , warns about things getting out of kilter…
It’s generally a good idea to find what’s causing problems and fix them, but sometimes the answer is to stop reporting the problem.
Amongst the things that are reported when you run a name service are the hosts tHat try to use your server as a recursive resolver (you don’t want to let anyone other than your own customers do this or you might become part of a DDoS attack) and the servers that give malformed responses.
Now as I run a pretty up-to date name server I tend to believe the server when it reports that it’s getting random responses, and had written code to collate the reports to make an exclusion list of servers not to talk to.
Top of the bad response list were ns?.msft.net. These are the name servers which connect you to hotmail.com and outlook.com, and while blocking them gives a noticeable improvement in SPAM volume, ultimately there are people who want to use Hotmail.com despite it’s dreadful record of accounts being hacked
Mail Problems after Email Server upgrade
by Andrew Macpherson on Oct.08, 2013, under Operations
Over the end of last week, and the weekend we had to make an Emergancy upgrade to the mail server. Fortunately for many this was transparent once the DNS had updated, however there are some customers who have email account names which differ from their email address
Mostly those customers can read their email but cannot send new mail
The workround, and I stress this is a workaround not a long term answer, is to add @assp.knots.net to the end of their account name in the sending mail section in the account configuration of your mail program, or the settings app on iOS. Longer term, please contact us at a convenient time for you, and we’ll rename your account to match your mailbox — this will also require setting your password again
Sorry for the nuisance, hope this gets you going
How to get your mail blocked
by Andrew Macpherson on Nov.30, 2012, under E-Mail hosting, Operations, SPF the Sender Policy Framework
We spend a lot of time trying to let legitimate mail through, and filtering problem mail into SPAM folders for our customers. Here are a few ways you can ensure you get filtered as SPAM
- Always change the sender of each message, to each recipient, to prevent whitelisting
- Assume that the FROM line will be recognised (it will not, sender is what counts)
- Have an incorrect SPF record for where you are sending from
- Always change the sender of each message, to each recipient, to prevent whitelisting
- Make sure your customers never reply to your mail, use a “noreply” address
- Send mail to customers who report you as SPAMMING them
- Use a 3rd party mailing list service with bought lists
- Send mail containing links to sites that are black-listed
- When doing any of the above, send lots of mail to establish a history of sending dodgy mail
- Always change the sender of each message, to each recipient, to prevent whitelisting
- Slightly less important, have a mismatch between the email sender’s domain, and the system sending it
- Carefully include keywords that trigger automatic traps e.g. “Beneficiary,” “winner.” “prescription,” etc
- Send from a misconfigured system
- Have an invalid Message-id, or none at all.
- Always change the sender of each message, to each recipient, to prevent whitelisting
- Send from a system with a dynamic IP address (home vs business broadband)
- Use words and phrases that differ greatly from the language written by the intended recipient (Bayesean check)
- And remember always change the sender of each message, to each recipient, to prevent whitelisting
After all, it’s all about tracking deliveries, not getting your message through isn’t it?
Poor Joomla Code, again
by Andrew Macpherson on Nov.13, 2012, under Operations
We were asked to install the current version of Joomla (2.5.8) for a customer. Should just be a moment’s work? Not so.
The people who wrote the install code try to do everything with absolute paths. This is fine if you are running on a single-use server. It blows up when one uses cgiwrap to protect the users of a shared server from each other.
To make matters worse, this “Absolute Path” gets calculated in many different places (why?), and I’ve mentioned that I consider Joomla to be totally object obfuscated, and just plain unmanageable before now…
Result: the install script tries to get the server to execute “.js” files, instead of downloading them as part of the page. The visible symptom is that one is stuck on the first install page (lacking the JavaScript to progress)
Solution: install on the sort of simple server the coders anticipated, then copy across, and fix up “live site” in the config file.
What a palaver
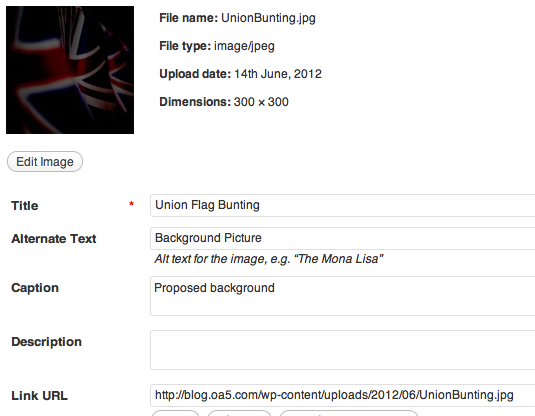
WordPress article background picture
by Andrew Macpherson on Jun.14, 2012, under Operations, Technology
Should be easy, right? Slight problem that the result is going to go under the article text, but not the heading, but this should suffice for most purposes.
As always with this sort of question the devil will be in the detail. For instance on our blog here the background is dark, so any background image also has to be dark or risk losing the text.
So with this image the problem is the white in the flag, a black layer and a hard light blend soon fixes that. Then upload the background, without inserting it into the post, but pick out where it is stored in the wordpress backend — see the screen shot
The Link URL text is by default the location of the image. Copy this, then cancel out of “insert image”. Now all you have to do is put in a little bit of raw html round your text.
Click the HTML tab at the top of the editor and at the top of your article paste in the url of your background in amongst some magic like this:
<div style="background-image:url(/wp-content/uploads/2012/06/UnionBunting.jpg);
background-size: contain; ">
The background-size: contain element matches the width of the image to your article width. You might also want background-repeat:repeat-y to repeat vertically or background-repeat:none to only put the image in once
At the bottom of your article you need to put in a matching </div> to end the area that will have the image
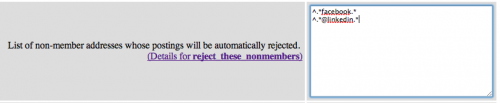
Social Network Nuisance E-Mail
by Andrew Macpherson on Feb.06, 2012, under E-Mail hosting, Operations
If there’s one thing that’s visible every day, it’s that users (& some administrators/developers) are easily confused.
Take for instance the “Find My Friends” misfeature on most Social Networking sites. None warn the user to go through and check that the invitations they are about to generate are really only going to their friends, and that they should only send mail directly to their friends, not to mailing lists.
I wonder how many suppliers get invitations to connect to customers whom they don’t really know on LinkedIn? How many mailing lists are invited to sign up and befriend FaceBook users? Some sites like Flickr limit their invitations to existing users, others need blocked from every mailing list.
Edimax Network Printer Port
by Andrew Macpherson on Jan.05, 2012, under Operations, Technology
After 10 years of use my Kingston Print server gave up the ghost for no discernible reason. At this point I discovered what a rare thing a parralel print interface had become. Still that was what was needed for my trusty old LaserJet 6MP (main virtue unchipped toner cartridges)
Quickly went on the net and found the Edimax PS1206P which plugs straight into the parallel port, and presents an RJ45 socket for the network lead. Unfortunately it also has a wall-wart PSU, which is however switched on the low voltage side!
The only trouble with the unit is how the manual lies about the defaults. Rather than coming up with DHCP enabled as stated, it came up on 192.168.2.2. That was fun to find.
The validation on the advanced configuration is rather too well aligned with the low unit cost, but now configured it is working nicely. If you use windows, and don’t worry about what you are doing it will work well for you.
Microsoft do not Phone
by Andrew Macpherson on Nov.07, 2011, under Operations
So when someone phones you up, saying they are a Microsoft Technician, or someone employed by Microsoft you can be sure it is a fraud attempt. I suggest you say “Hold on a moment, be right back” and put aside the phone without hanging up so that their bill keeps growing.
The current scam is quite clever. The caller will ask you to run a program “eventvwr” which will show you the log events handled by your operating system in normal operation. They will then try to convince you this demonstrates a problem that you should pay them to help you fix.
Typically they will ask for £49 for a program for you to download. This is a really bad idea, you do not want this malware on your computer, or to give them your credit card number.
Microsoft have a system called “Microsoft Updates” for sending you patches and fixes , which you should be running regularly anyway,and the £50 the caller is asking you for is about the same amount that you paid for the Windows Operating System, bundled with your computer.
Just plug it in
by Andrew Macpherson on Oct.30, 2011, under Operations, Technology
Sometimes I don’t think English is adequate.
“Here it is, I’ve configured it for you, you just have to plug the bits in.” I said. Unfortunately I made the mistake of leaving all the ancillary bits in the box. Next thing I hear is it coundn’t fit as there were no ports. Router has 4 ports, 1 PC, 1 printer, 1 cable for laptop therefore 1 spare port. “Huh?”
Then I hear “It kept getting to a screen, then not going any further.” I should have confiscated the CDs.
This customer is extremely intelligent, but gets annoyed, and feels their mental competence is being attacked, whenever one attempts to diagnose a problem. They definiely will not pick up the phone to ask, which is why I spent 3 hours making sure that all they had to do was
Just plug it in
Hotmail ignoring MX records
by Andrew Macpherson on Sep.02, 2011, under E-Mail hosting, Operations
One of my customers reported a very focused failure.
They could not receive emails from Hotmail. Everywhere else seems to be fine, just hotmail returned immediate failure when mail was sent to them. The same hotmail account could send mail to us, and to other customers.
The thing that was different with this customer was an A record for their domain, a practice I try to discourage, because I could see this happening with mails from out of date systems, but as far as I was aware, not an issue with major providers. The customer has the domain-level A record because their website supplier thinks it uncool to use www. in front of the website (a mistake made by WordPress-mu as well)
It was very simple to demonstrate the fault. We removed the domain level A record from the DNS and the mail immediately started to come through.